Executive Summary:
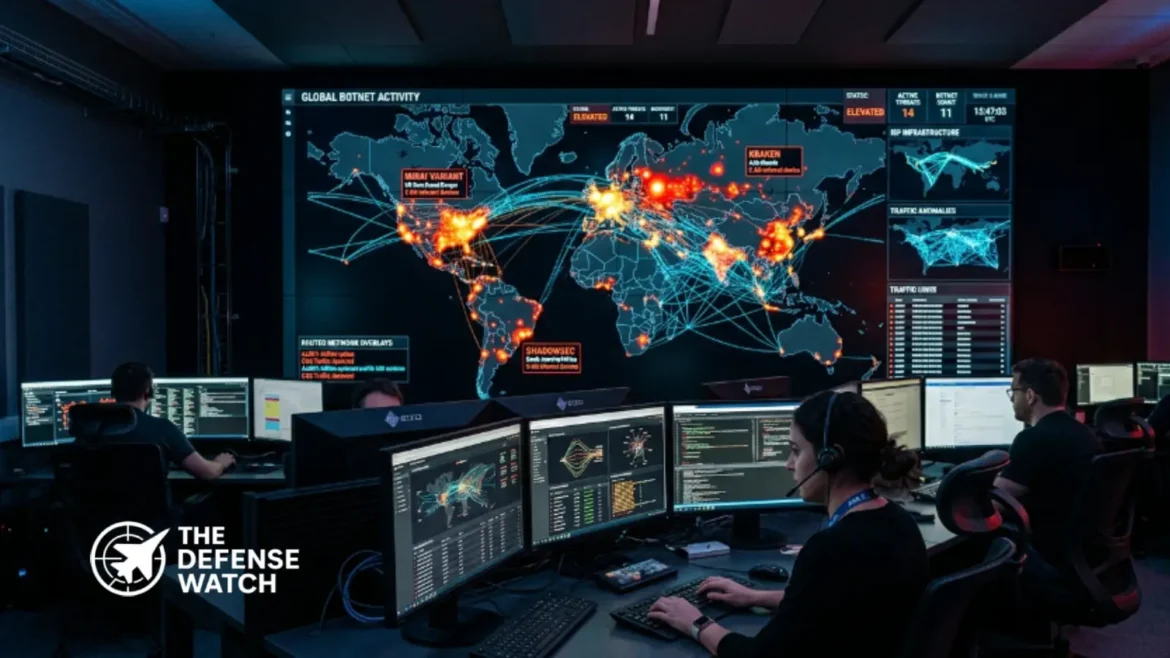
The UK’s National Cyber Security Centre (NCSC) has warned that China-linked cyber actors are increasingly using covert botnet networks built from compromised internet-connected devices to conduct espionage and cyber attacks.
The advisory, issued with international partners, highlights growing concerns over threats targeting UK organizations and critical infrastructure.
NCSC Warns Of China-Linked Botnet Threats Targeting UK Networks
The National Cyber Security Centre has issued a new warning about large-scale China-linked botnet operations targeting organizations in the United Kingdom and allied nations.
According to the advisory, Chinese state-linked cyber actors are increasingly relying on covert networks made up of compromised routers, internet-connected devices, webcams, firewalls, and smart technologies to conceal malicious cyber activity and launch attacks against strategic targets.
The warning was released jointly with cyber agencies from the United States, Australia, Canada, Germany, Japan, New Zealand, the Netherlands, and Spain during the CYBERUK 2026 conference in Glasgow.
Officials said these covert networks, often referred to as botnets, are becoming a preferred operational method for China-linked cyber groups because they provide anonymity, scalability, and plausible deniability.
Shift Toward Covert Networks Raises Strategic Concerns
The NCSC stated that Chinese cyber actors have shifted away from individually controlled infrastructure and now increasingly depend on massive networks of hijacked consumer and commercial devices.
These networks allow attackers to conduct reconnaissance, malware delivery, command-and-control operations, and data exfiltration while masking their origins behind ordinary residential internet traffic.
The advisory noted that a single covert network may be shared among multiple threat groups simultaneously, complicating attribution and making traditional cyber defense methods less effective.
The NCSC also warned that many compromised devices involved in these networks are outdated or unsupported products that no longer receive security patches from manufacturers.
Among the examples highlighted was the so-called Raptor Train network, which reportedly infected more than 200,000 devices globally and was linked to the Chinese company Integrity Technology Group.
Western intelligence and cybersecurity agencies have previously linked China-based groups such as Volt Typhoon and Flax Typhoon to campaigns targeting critical infrastructure and government networks.
Critical Infrastructure Remains A Key Concern
The latest warning reflects broader concerns inside the UK and allied intelligence communities about state-backed cyber operations targeting national infrastructure.
NCSC leadership recently stated that the UK is now handling roughly four nationally significant cyber incidents every week, with many linked directly or indirectly to hostile state actors including China, Russia, and Iran.
Security officials warned that sectors including transportation, telecommunications, energy, water systems, defense supply chains, and public services remain attractive targets for advanced persistent threat groups.
China-linked cyber activity has become an increasing focus for Western cybersecurity agencies over the past several years. Earlier advisories from the NCSC and Five Eyes partners highlighted campaigns exploiting small office and home office routers as launch platforms for espionage operations.
The latest advisory indicates these techniques are now being used at much larger scale and with greater operational sophistication.
Why The Threat Matters Beyond The UK
The NCSC assessment carries significance beyond Britain because many of the compromised devices used in covert botnets are distributed globally.
Security researchers and allied governments believe these networks can be rapidly rebuilt as devices are patched or disconnected, creating what cybersecurity experts describe as “IOC extinction,” where indicators of compromise disappear before defenders can effectively block them.
This evolution presents a growing challenge for traditional cybersecurity approaches that rely heavily on static IP blacklists and fixed threat signatures.
The advisory also reflects wider geopolitical tensions surrounding cyber operations linked to state-sponsored actors. Recent Western intelligence assessments have repeatedly identified cyber capabilities as a central component of strategic competition between China and Western nations.
For defense and national security planners, the warning underscores how civilian digital infrastructure and everyday connected devices are increasingly becoming part of the broader cyber battlespace.
Recommended Defensive Measures
The NCSC urged organizations to improve visibility over internet-connected devices and strengthen monitoring of remote access infrastructure.
Recommended actions include:
- Replacing outdated routers and unsupported hardware
- Applying firmware and software updates immediately
- Enabling multi-factor authentication
- Monitoring unusual outbound network traffic
- Segmenting networks to isolate vulnerable devices
- Using dynamic threat intelligence feeds instead of static IP block lists
Cybersecurity officials also emphasized that critical infrastructure operators should review resilience planning and incident response procedures in anticipation of increasingly sophisticated state-backed cyber campaigns.
Get real time update about this post category directly on your device, subscribe now.